What is VM GenerationID identifier?
Very simple description of the VM Generation ID is that Generation ID is a protection of your Active Directory against restore of a checkpoint (snapshot) of a virtualized Domain Controller (DC). As you can imagine if you restore a checkpoint of a DC (you do not restore a backup, you just revert DC in time by checkpoint restore) you can significantly cripple whole Active Directory.
From my point of view you should never ever use checkpoints on production VMs. Your Junior Administrators should not be a Hyper-V or System Center Virtual Machine (VMM) Administrators with ability to create or restore checkpoint. But in the past many enterprises were damaged by restore of a checkpoint of virtualized DC and therefore Microsoft brought VM Generation ID.
Active Directory stores the VM GenerationID identifier as part of the msDS-GenerationID attribute (no replication by default) on domain controller objects. When a checkpoint is restored the VM Generation ID is automatically changed by the hypervisor. When the change is detected then DC will reset the invocationID, discard (flush) the RID pool and updates msDS-GenerationID with the new value. The DC behave like it was restored from a backup.
AD DS Virtualization Safeguard in test environment
In test environment the AD DS virtualization safeguard is very irritating. I very often use checkpoints in test environment including environment with multiple DCs and multiple member servers.
I often shutdown all VMs in a single environment and then I checkpoint them all. This is mean that I have saved consistent point in time on the whole environment. I can later restore all checkpoint on all VMs. I call it Active Directory Forest Recovery (this is joke).
This is not possible with Generation ID aware AD DS or hypervisor. Of course it is possible to fix AD when you restore a checkpoint of a multiple DC but checkpoints should be simple and quick and the fixing is not quick.
Process to disable VM Generation ID – Only for testing purposes, do not do it in production environment
- You can see the current VM Generation ID in XML configuration file of a Hyper-V virtual machine.
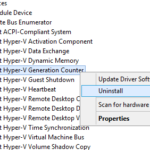
- In guest OS in Device Manager you can see Microsoft Hyper-V Generation Counter system device.
- The driver for Generation Counter is: %SystemRoot%\System32\drivers\vmgencounter.sys
First possibility: Disable device (nice and clean way)
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\gencounter] "Start"=dword:00000004
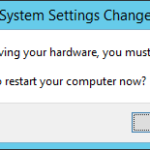
- And then after restart a nice warning message shows up.
- Now it is possible to disable whole device but it is not required to do it.
Second possibity: Remove driver (ugly way but this is also possible)
- To disable Generation Counter you can uninstall the device.
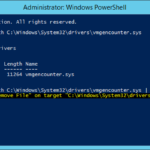
- But before the restart the SYS file has to be removed because in otherwise the OS will install it again after the reboot.
- You can remove it using PowerShell and then you can restart the VM.
Remove-Item -Path C:\Windows\System32\drivers\vmgencounter.sys -Force
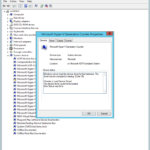
- It is possible to see a warning in Device Manager after the restart that is caused by missing driver (SYS file).
Test that Active Directory Virtualization Safeguard
- Now in testing environment you can shut down all VMs, create a checkpoint and then restore it to test that Generation ID was disabled.
- After the checkpoint restore it is possible to check the current Generation ID in VM XML configuration file. The ID should be different.
- The simplest way to test the modification is to create “something” after restart of the DC that was restored from checkpoint. If your RID pool was flushed then you will not be able to create for example an user object.
P.S. I would like to thank Pavel Formanek (Premier Field Engineer at Microsoft), who helped me with locating a driver that needs to be removed.











2 responses to “How to disable Virtual Machine Generation Identifier (VM Generation ID) on Domain Controller on Hyper-V 2012”
Thanks for this awesome guide. I realize, it is only 5 years old 🙂
What would this look like for VMware?
Also, can I clone a VM with VM-GenerationID disabled and have 2 VMs exist in the same environment?
Thanks again
Dear Rudolf,
Thank you so much. You helped me a lot with dsamain.exe issue to start a NTDS backup I wanted to verify. After fixing the database I got stocked here. I followed you steps to disable the driver from REG and reboot. After restarting and running the dsamain.exe again I worked. I could complete now the checks I wanted to perform. Many thanks!